The npm install and npm audit commands check for vulnerabilities against known security risks reported in the public npm registry and is an essential step in protecting yourself from software supply chain attacks.
Read More
Eyalkatz submitted the following stories to BizSugar
Read Jit Blog Post: NPM Audit: 5 Ways to Use it to Protect Your Code
From https://www.jit.io 469 days ago
Essentials for Real-Time Data Streaming Architecture

From https://equalum.io 470 days ago
Made Hot by: thecorneroffice on January 29, 2023 12:15 pm
Real-time data streaming is the constant flow of data produced by multiple sources. It enables you to collect, analyze, and deliver data streams as they generate in real-time. The architecture your choose has significant implications for how your systems operate. Learn more with Equalum.
Read More
10 Learning & Development trends for 2022
From https://www.thehrdirector.com 479 days ago
Made Hot by: logistico on January 19, 2023 2:58 pm
When you have skills to teach and workers who want to learn, the last thing you want to do is squander the opportunity by falling back on minimally engaging traditional educational programs. Here are ten Learning and Development trends for 2022 that point toward better educational solutions which r
Read More
Top 5 Automated Restaurant Ordering Systems for 2022 - Hi Auto
From https://hi.auto 483 days ago
Automated order taking replaces manual tasks with technology to free up employees’ time. Discover Top Automated Restaurant Ordering Systems.
Read More
10 Innovative Ideas for Employee Development -
From https://hourone.ai 484 days ago
Made Hot by: PMVirtual on January 14, 2023 1:10 pm
When kids come home from school at the end of the day, we ask what they learned. We hardly ever ask adults what they learned at work that day, but maybe we should. Employee development programs help your best workers feel confident, expand their skillset and advance their career goals.
Read More
Clone Phishing Attacks: 3 Ways To Protect Your Organization
From https://www.memcyco.com 486 days ago
Clone phishing, a well known attack, infamous for often going undiscovered for a considerable time and taking a long time to resolve. Protecting your organization from phishing attacks can be a huge boon.
Read More
Clone Phishing Attacks: 3 Ways To Protect Your Organization
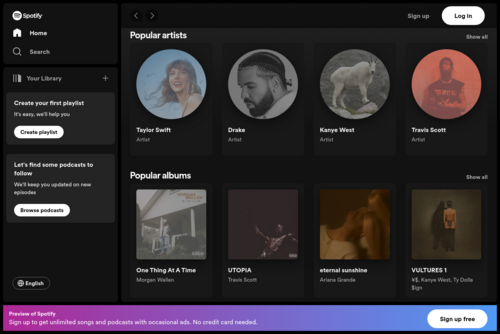
From https://open.spotify.com 489 days ago
Clone phishing is one well-known form of such attacks, infamous for often going undiscovered for a considerable time and taking a long time to resolve. Our solution protects from attacks on every touchpoint between your brand and its customers, partners, and employees.
Read More
21 Sentences That Mean Your Startup Is in Trouble
From https://mvpgrow.com 493 days ago
Made Hot by: luvhealthcare on January 5, 2023 3:23 pm
A failing startup will exhibit one or more “tells” a sharp player will notice, then immediately move to hedge their bets elsewhere. Surprisingly, one of the most obvious failure “tells” is found in the language that the startup uses.
Read More
7 Must-Have Steps for Production Debugging in Any Language - Lightrun
From https://lightrun.com 505 days ago
Made Hot by: bloggerpalooza on December 25, 2022 9:20 pm
Production debugging identifies the underlying cause of issues in an application in a production environment. Learn with Lightrun.
Read More
Web Application Security: What to Consider for 2023 - Spectral
From https://spectralops.io 506 days ago
Made Hot by: mikehartman1 on December 24, 2022 10:05 am
Web AppSec is a software security paradigm that enforces security controls to protect websites, web applications, and assets from cyber threats. It demands that developers build resilient applications that can withstand sophisticated cybersecurity attacks. Here are the basics.
Read More
Subscribe
![]() “Rachel: Great to hear! Thanks for your kind words! :)
All the Best,
Martin...”
“Rachel: Great to hear! Thanks for your kind words! :)
All the Best,
Martin...”
![]() “Thank you, Martin. That's a fantastic motto... and I couldn't agree more!...”
“Thank you, Martin. That's a fantastic motto... and I couldn't agree more!...”
![]() “Lisa: Good to hear! Thanks for your response....”
“Lisa: Good to hear! Thanks for your response....”
![]() “For sure, I know I did years ago when I was working for others....”
“For sure, I know I did years ago when I was working for others....”
![]() “Lisa: I wonder if they potential employee is doing a background check on...”
“Lisa: I wonder if they potential employee is doing a background check on...”







